No need to be paranoid about it, but integrity and security should be concerns for everyone who uses a Learning Management System on a regular basis. Learning professionals must counter threats to the integrity of both system infrastructure and the content placed on that system. This isn’t just the responsibility of the admin. It’s a regular practice to embed into the fabric of an educational community.
There is a common and somewhat understandable misconception about how the size and complexity of an eLearning environment relates to the challenge of ensuring structural integrity. The reality is, a bit of proper planning is all it takes to make security a scalable practice for your community. In this article, you will find a basic set of practices that will give you a bit more confidence that you’re running an “indestructible” LMS in practical and affordable ways.
№0. Before you start: Understanding people’s aims and motivations (including your own)
It makes sense to set some ground rules and clear definitions before we begin. Some might find terms like “safety,” “security” and “integrity” interchangeable, while other struggle to see the connection between them. Here are the ways we will think of these and other terms going forward.
- Safety: A broad, psychological concept related to the person or user’s perceived state. In the context of an LMS, the user feels safe if they can trust that the system will not take advantage of them or their information, that it will not let anyone be able to; and that using the LMS will not cause any type of harm or represent a threat, to them or others.
- Protection: A specific measure, either active (“always on”) or available to a user, to avoid, minimize or reduce harm.
The more and better protections measurements are available, the safer the LMS will be. - Security: The set of processes, practices and available measures through which the LMS can guarantee a response against a threat or vulnerability.
The security of an LMS depends on how well the protections it features cover a sufficient breadth of possible threats. Good security is a requirement, not necessarily a guarantee, for safety. - Risk: The potential harm a given threat can cause. The concept of risk encompasses the threat alongside its likelihood of happening, the severity of consequences should it happen, and the average cost to manage the risk over a period of time.
An LMS is safe to the extent that it is able to manage risk. Since it is impossible to perfectly protect an LMS, sensible risk management prioritizes protections that tackle the costliest threats, thus maximizing security. - Defense: It refers to both the mechanisms and the professional practice of security, tasked to ensure proper measures are in place and that proactive approaches are continuously adopted.
Active risk management and analysis is the ultimate objective of defense roles. Implementation and enforcement of protection measures, a main defense duty, determines the level of security of an LMS. Communication and leadership regarding defense operations determine the sense of security among users. - Integrity: It refers to the ability to keep LMS data consistent and accurate in an LMS, and the capabilities to identify instances of undue data manipulation or alteration, recover data and system status, and anticipate threats and sources.
The outcome of proper security, risk management and defense is integrity.
Right now we’re going to focus on integrity, both as the resulting outcome of proper defense and risk management; and as the area where the responsibility extends beyond leaders or admins. Which in a way makes it the most fragile.
Before continuing —or actually starting—, we believe it is important to emphasize the role people play in
№1. Like CAPTCHA, but better: set a similar human verification method
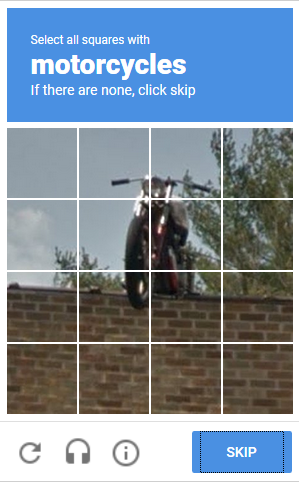
A ground-level measure, CAPTCHA, hCAPTCHA, reCAPTCHA and similar tests are designed to remove the option for bots and malicious actors to guess username and password combinations by brute force. All modern LMSs provide a straightforward way to enable a CAPTCHA-style verification service from a trusted provider, either natively or through a plugin or integration.
The latest generations of generative AI have demonstrated their ability to deduce CAPTCHAs. Some vendors, like ChatGPT, include safeguards that prevent regular users from accessing the AI’s abilities. But researchers have been able to override ChatGPT’s safeguards.
It is time to (always?) look at the next generation methods of human verification. Newer methods tend to focus less on things humans can do that robots cannot, the list of which might be zero by the time you’re reading this; and more into ways humans typically behave, that robots haven’t emulated. Multi-factor authentication, as we’ll see below, are also common replacements to CAPTCHA-like techniques.
№2. Allow concurrent logins from the same user only under certain conditions

Learning platforms often allow a student to only be active on one device or browser at the same time.
It’s usually assumed that a student has no reason to be simultaneously online on more than one device. From an infrastructure perspective, preventing concurrent extra logins helps manage server load, allowing you to control usage and reduce associated costs. Arguably, a single-device rule improves student focus too.
In an LMS where offline access is allowed —as it is the case with content download features in some of the best LMS mobile apps—, concurrent access to the environment, online and offline, may not be preventable.
There are legitimate reasons why concurrent logins are desirable, however, both from a user experience (UX) and an educational perspective. The student may find it more convenient to use two or more devices. They could be using a second device to look at the course materials for their work on a given research project, workshop, or assignment. For example, a language course may offer supplementary documents, like conjugation tables, that they can access from the app handily.
To avoid compromising on integrity and usability, it would be better to apply a set of conditions for multiple logins. These could include allowing concurrent logins from nearby IP addresses, or blocking traffic from more than one country.
If your LMS has a concurrency limit in place, make sure the community is aware, as the limit may undermine the user experience or lead to lost data from unsaved work.
№3. Consider applying IP address limitations or restrictions
When well implemented, monitoring Internet Protocol addresses can be one of the simplest, most effective security controls you can put in place. Of course, IP address filtering usually works best when part of a set of measurements.
Since IP addresses are related to geographical region, begin by quickly filtering out places you can guarantee no actual user will access from. You can also consider blocking unusual locations identified as so-called “roots of evil”.
It’s also possible to find a list, or subscribe to a service that identifies addresses as malicious or “flags” them, to include in your blacklist.
If you do implement IP restriction by country, survey your community for VPN use. VPNs obscure the original IP of the user, replacing it with an address from a country of the user’s choice. You might want to notify them about any restricted IPs.
№4. Implement Multi-Factor Authentication

Double (2FA) and Multi-Factor Authentication (MFA) methods have become a widespread, mildly inconvenient though ultimately accepted extra hurdle for members of digital communities, educational being no exception. With 2FA or MFA, when you log in from a non-recognized device or browser, you are asked to enter an additional code or perform an action sent via email, text, or an app in a different, recognized client. Other methods involve a “dongle,” an exclusive USB drive or key (such as the infamous YubiKey). Though some users may find the extra effort a little irritating, research has shown that MFA considerably curtails the rates of phishing and targeting attacks.
Any text or email-based MFA implementation will require a solution provider capable of sending codes as quickly as possible to the user. The responsiveness of the MFA procedure requires permanent attention to ensure all users—and only the intended users—can easily access your platform.
№5. Encrypt your data
Where data access should be restricted to specific users, encryption methods are standard practice. It is also possible for applications to encrypt their whole database. When parts of the application database are encrypted, not even high-level admins—or government-funded hackers—can meaningfully obtain private data without the key to decrypt it, at least not in a humanly reasonable amount of time. Quantum computing could alter the paradigm. In the meantime, it is common practice to use information only the user holds, such as a password, or some “token” generated by the authenticating device, as the decryption key.
№6. Automated monitoring for suspicious and malicious behavior

More commonly implemented where data sensitivity or the consequences of malicious conduct are more onerous, data-based solutions add pattern-matching, real-time statistical analysis, machine learning, and AI methods where standard measurements are not enough. Common use cases in education include e-proctoring, for high-stakes examination.
Techniques like “SIM Hacking” have proven capable of bypassing MFA protections. A poorly implemented policy regarding lost devices, for example, may present fatal vulnerabilities. Or a user device could get infected by malware that disables one or several protective measures.
Arguably, there is no weaker point of failure than users themselves. Targeted individuals may neglect a device for just enough time to be maliciously overtaken. They may use a compromised network. Or they can leave their password written on a post-it note stuck to a monitor when images of their office are being broadcast nationwide. And then there’s the most insidious threat to cybersecurity in recent times: social engineering.
This family of security methods are not, to our knowledge, available for specific LMSs. Rather, they are implemented at the server level. Amazon Cloudfront is a famous solution, as are Cloudflare, Akamai, and vendor-specific ones in Azure or Netlify.
№7. Provide security, social engineering protection training
To fully consider the integrity of an environment, all factors must be taken into consideration—including the users of the system. There are currently no known wholistic integrity antidotes that act as adequate replacements for user awareness and skills.
The evolution of UX thinking has led to clever tactics that embed knowledge into interfaces. Certain designs can, for example, prime the user into being careful when they’re about to make a sensitive action. But basic concepts, known vectors of attack and security measures are topics users can always acquire more effectively, even if they can never fully avoid them.
Because of its psychological, social and technical ramifications, social engineering can be a fascinating, multidisciplinary subject. Likewise, sound competencies can lead to positive ramifications, like a better awareness of your own cognitive biases, or common flaws in the design of communication systems. Given that most of the exploits aim to impersonate someone with some authority within a group, community-based topics and training can be especially effective.
There are a variety of security and social engineering education alternatives in the market, both generalist and LMS specific. The ability to embed learning into the interfaces, or more generally reduce security best-practice friction, tends to improve effectiveness in more modular, flexible or open source platforms.
№8. Comply with data protection measures

There’s a lesser known benefit of GDPR and the wave of data protection regulation it sparked: The movement among LMS developers to create better tools that help ensure compliance, respond to requests more quickly and offer a more manageable overview of systemic integrity.
In Open LMS and Moodle™-based systems, comprehensive policy and data management dashboards are available. Admins can keep track of the policies a site must implement, their versions and user acceptance status. When users request a download of all their LMS data, from activity to grading and performance, to chat messages and forum posts, the system makes it easy to get ahold of all data by requiring all relevant sections of the site to go through a Privacy API that keeps track of everything. This tool also allows full erasure requests.
Privacy controls—and proper user education on them—can become a powerful cultural booster for awareness regarding the location of personal information and proper security and integrity measures.
№9. Conduct regular audits

Some define cybersecurity as a cat-and-mouse game. As security researchers and staff surveil systems and explore technologies, they alert the public about new threats. They also discover glaring loopholes likely to become attack vectors that have remained hidden for decades.
In any case, security and system integrity in an LMS isn’t merely a goal to accomplish, but a wider community practice that takes consistent, regular promotion, education and practice.
An LMS integrity audit begins by defining a scope. Naturally, a broader and more detailed scope, focusing on the several dimensions of integrity—human and otherwise—offers greater reassurance about the effectiveness of the audit. Once a scope is defined, common steps that follow include:
- Documentation review, covering technical documentation, designs, user manuals, policies and procedures
- Analysis of system controls, permissions and user access
- Analysis of system logs or monitoring tool reports, possibly including forensic analysis for the integrity of monitoring data, if tampering threats are credible enough
- Generalized data integrity verification methods across the whole scope of the audit
- Backup comparisons and restoration testing
- Penetration testing, and other “white hat” approaches to probe into the system’s existing measures and rules. This includes keeping the techniques up to speed with the current state of the art
- Reporting and follow-up
In the case of well-populated open source systems, integrity audits can benefit from outcomes and reporting from fellow users. Several instances of reported issues in open source LMS software such as Moodle™ involve an independent developer flagging a situation which is quickly addressed and patched for millions of users worldwide. Overall, shared auditing might just be the single most powerful factor behind the dominance of open source software, from operating systems to utilities and libraries, in server infrastructure.
To sum up
Safeguarding the integrity of a learning environment is a multi-pronged exercise that may be spearheaded by an LMS admin or a security manager, but one that only has realistic odds of success through a community approach. It consists of an active process that keeps design and development, rules and procedure, user education, and auditing steps up to date.